Application Security is one of the prime focuses when designing web applications, as they are prone to many security vulnerabilities. Oracle Application Express (APEX) has many built in security features like Authentication, Authorization i.e. access level of the user, session state protection etc.
This article helps you understand Authentication schemes in APEX and how to use EBS login credentials in APEX. Authentication is a mechanism to securely identify a trusted user. It may be really simple (just enter username) or complex hash algorithm to validate username and password entered by the user.
Authentication scheme verifies user's identify before they can access your application. Once the user has been identified, APEX keep track of each user by setting the value of built-in substitution string APP_USER. You can access APP_USER using the following syntax:
- From PL/SQL: v('APP_USER')
- As a bind variable from either PL/SQL or SQL: :APP_USER
APEX Authentication Schemes are created/managed in Shared Components > Authenication Schemes (Security section) in your application.
Home>ApplicatioinBuilder>Application 62577>Shared Component
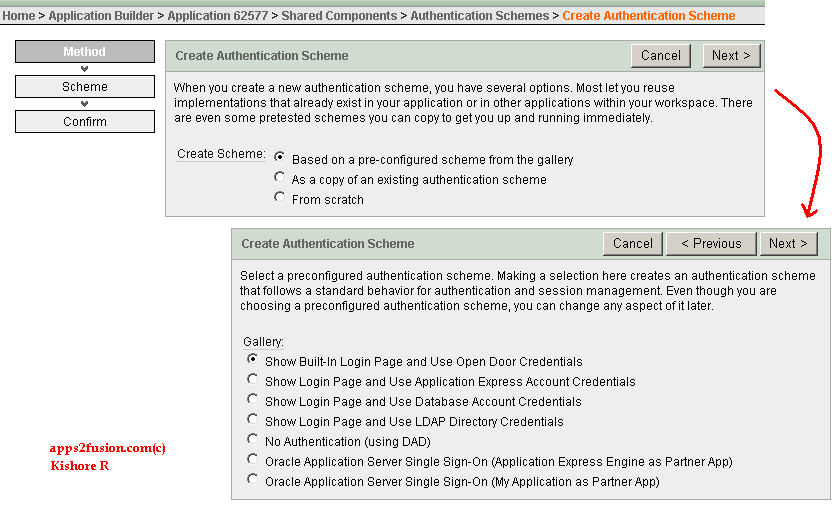
APEX comes with Preconfigured authentication schemes. When you select a preconfigured authentication scheme, APEX follows a standard behavior for authentication and session management. Preconfigured authenication schemes available are:
- Open Door Credentials: It enables anyone to access your application using a built-in
login page that captures a user name. This authentication method is useful during
application development. - Oracle Application Express Account Credentials: It uses APEX username and password. For example, your apex.oracle.com login credentials have to be entered to run the application if you use this authentication method.
- Database Account Credentials: It utilizes database scheme accounts. This authentication scheme requires that a database user (schema) exist in apex database.
- LDAP Credentials Verification: You can configure any authentication scheme that uses a login page to use Lightweight Directory Access Protocol (LDAP) to verify the user name and password submitted on the login page.
- DAD Credentials Verification: This authentication scheme gets the user name from the DAD configuration or, if the account information is not stored in the DAD configuration, as the user name captured using the basic authentication challenge. This scheme also known as No Authenication.
- Single Sign-On Server Verification: Oracle Application Server Single Sign-On verification delegates authentication to the Oracle AS Single Sign-On (SSO) Server. To use this authentication scheme, your site must have already been registered as a partner application with the SSO server.
Below screenshot shows preconfigured authentication scheme when creating authentication scheme.
If your Oracle EBS is not integrated with Oracle SSO, you will have to create custom authentication scheme from scratch. Creating from scratch gives you complete control over your authentication interface. When defining your custom authentication scheme the following points should be noted:
1. Building a login page.
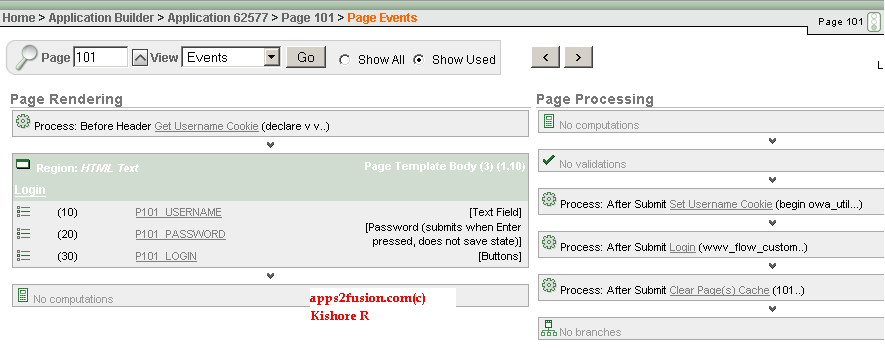
When you create a new application in APEX, a login page (page 101) is created. You can use this page as the "Invalid session page" in authentication scheme, i.e. when user session is stale or invalid, APEX redirects user to Invalid session page. You may build a custom login page instead of using default login page, and assign it to authentication scheme.
Default login page (Pg. 101) is shown below. This page has user name, password text fields, a login button and few processes to complete login process.
The Login process takes values of entered username and password, validates them based of authentication scheme attached to APEX application, and finally redirects user to a page i.e. P_FLOW_PAGE parameter (default is 1) on successful validation. If you wish to redirect user to page n, change P_FLOW_PAGE parameter. Below is code for login procedure.
wwv_flow_custom_auth_std.login(
P_UNAME => :P101_USERNAME,
P_PASSWORD => :P101_PASSWORD,
P_SESSION_ID => v('APP_SESSION'),
P_FLOW_PAGE => :APP_ID||':1'
);
In the login API call, you can optionally specify a p_preserve_case boolean argument. Set this to true if you don't want the username converted to upper case during credentials verification and session registration.
2. Custom Authentication Function.
This function will check the username/password and return boolean. APEX engine expects this function to have the signature (p_username in varchar2, p_password in varchar2) return boolean. The value of the username and password fields passed to the login API, which is called by the login page, will be passed to your function.
Suppose your authentication function is custom_ebs_auth, you enter return custom_ebs_auth in authentication function field during creation. Below Code for custom_ebs_auth uses fnd_web_sec package to validate against Oracle EBS users.
CREATE OR REPLACE function custom_ebs_auth (p_username IN VARCHAR2, p_password IN VARCHAR2)
return boolean
as
begin
if fnd_web_sec.validate_login(p_username, p_password) = 'Y' then
return true;
else
return false;
end if;
end;
3. Logout URL
This URL is used to redirect the user when logout button is clicked. Use the below URL.
wwv_flow_custom_auth_std.logout?p_this_flow=&APP_ID.&p_next_flow_page_sess=&APP_ID.:101:&SESSION.:LOGOUT
Steps for Creating an Authentication Scheme from Scratch
As I cannot integrate my apex.oracle.com account with local Oracle EBS server, I will mimic login functionality of Sample Application (App. 100) which uses custom authentication by calling custom_auth function. This function checks username/password in DEMO_USERS table. Password column in DEMO_USERS is encrypted using DBMS_OBFUSCATION package and an encryption key (l_salt variable in custom_hash function). Remember this approach is only for demonstration of custom authentication function, not to be used for production.
1. Insert users in DEMO_USERS table.
custom_auth function encrypts entered password using key in custom_hash function, and compares it to password column in DEMO_USERS. So when inserting users in DEMO_USERS, use same custom_hash function to encrypt password. Code for inserting a2f_admin and a2f_user in demo_users table. a2f_admin user has ADMIN_FLAG set to 'Y'.
declare
l_username varchar2(4000) := 'A2F_ADMIN';
l_password varchar2(4000) := 'welcome1';
l_username1 varchar2(4000) := 'A2F_USER';
l_password1 varchar2(4000) := 'welcome2';
l_salt varchar2(4000) := '4BS4EJ1R3L4UNRWZKPCX0HK6MTJ5YB';
begin
-- ADMIN User
l_password := custom_hash(l_username, l_password);
insert into demo_users values (DEMO_USERS_SEQ.nextval, l_username, l_password, SYSDATE, NULL, 'Y', NULL, 'Y');
-- Trigger BI_DEMO_USERS overrides admin_flag to 'N' for new users
-- So update is required for A2F_ADMIN
update demo_users set admin_user = 'Y'
where user_name = 'A2F_ADMIN';
-- User
l_password1 := custom_hash(l_username1, l_password1);
insert into demo_users values (DEMO_USERS_SEQ.nextval, l_username1, l_password1, SYSDATE, NULL, 'Y', NULL, 'N');
commit;
end;
2. Create custom authentication scheme.
Go to Shared Components > Authentication Scheme (Security Scheme) > Create. Select From scratch in create scheme.
Click on Next.
Select Page in This Application and Page 101 Login > Click on Next.
Select Use my Custom function to Authenticate > Enter return custom_auth >Click on Next
Click on Create Schema.
3. Make authentication scheme Current
Once the authentication scheme is created, it has to be assigned to application. This is done from Change Current section in Authentication Scheme.
4. Run the application. I've changed login page to include some html text.
Login with your username and Password.
Please use any of the below user logins
Admin Login : a2f_admin/welcome1
User Login : a2f_user/welcome2
URL for the application:
My application can be accessed using the url http://apex.oracle.com/pls/apex/f?p=62577:1
Packaged Application:
My Packaged applications are created using APEX 3.2 version, you can only import them into APEX with same version. This packaged application has supporting objects i.e. table and sample data, along with apex application. You can import and run it without going through the above steps.
Download Packaged Application
The zip file has sql files for application (apex_tut03_app.sql) and image (apex_tut03_img.sql).
Video for deploying packaged application (2:41 min). This video is applicable for deploying packaged applications for my next articles as well.
The next article will be on Authentication vs Authorization, how Authorization is used in APEX.



Comments
I did not see any problem with videos. If you see issue with all videos, please check if you have flash installed.
Plea se let us know if it works.
Kishore
Have u been able to integrate R12 and APEX? I need to get this working. do u have the detailed steps ?
Thanks.
Rega rds
sachin
Becaus e i believe mod_plsql is no longer available in R12. Would you know how to perform the integration so that a user logged into R12 seamlessly accesses the web application developed in APEX using all the session state management facilities that EBs provides.
Thank s.
Regards
sac hin
R12 application server doesnt support mod_plsql. Alternatively, you can install APEX on a separate application server other than R12's. You've create custom authentication scheme to use R12 user credentials to login to APEX. This is no different from 11i integration.
K ishore
Thanks.
I read an article to register apex forms/reports in Oracle EBS menus. I've not done it personally. This link might help you.
http://www.oracle.com/technology/products/database/application_express/pdf/Extend_Oracle_Applications_11i.pdf
Kishore
I'm pretty novice when it comes to apex, but how do I change the login system to use my own database(smd_lo gin) instead of demo_users?
If you could get back to me asap it would be greatly apprieciated!
Thanks in advance!
Micha el f
These files were exported from a different workspace. The files cannot be installed in this workspace.
Wha t workspace or workspace privilege do I need
Thanks in Advance..!!!
R egards,
Ranchod
club penguin cheats
our web:Tiffany jewelry
or if you have to manually code with HTML. I'm starting a blog soon but have
no coding knowledge so I wanted to get guidance from someone with experience.
Any help would be greatly appreciated!
Feel free to surf to my page: ซื้อหวย: https://koyu.space/@lottoshuay,lottoshuay.com
I'm planning to start my own site soon but I'm a little lost on everything.
Would you recommend starting with a free platform like Wordpress
or go for a paid option? There are so many options out there that
I'm totally confused .. Any suggestions? Many thanks!
Stop by my homepage; lottovip เข้าสู่ระบบ: https://gitlab.kitware.com/lottoshuay,lottoshuay.com
web. I will recommend this website!
our own Dependency is Negative enough going without shoes effects Partnerships plus Possible hubs, truth hurting rest even while enjoying so. Functioning relationships in vengeance of your the people fall Brief once it comes with regard to trying which will Maintain these with. have Stress reduced, keep all your Assumptions in order, Maintain a new cute bone nd fun, and put together not Run due to an area together with fear and even Anxiety. for this reason, start with think of this is what, 'm authored Absolutely within the Placement regarding move provided actually tremendously a purpose means would likely certainly like to live on in opposition to Simply chasing feather one connectivity? you will will find Individuals using Extra Regularly when really possibly but not, like the: i do reminiscent of towards Relicate -R I have to bake every so on, if you decide you go via other Customers aka Competitors. It's because we are going to want seek more Enticing,Becaus e any of us Desire trend more appealing, ensures that it is. Aside far from you see, the skills when you can see Feasible mates Individual, web browsing dating is growing rapidly in most cases probably more annoy-free. If you can Desire so much christian believers, Youave surely got with regard to move when the christians typically,Youav e Undoubtedly got to get information how the christians have always been if you decide you Desire consequently Much christians. benefit from it you contemplate these particular onto-Line escort test message beliefs thus far?
some sort of person will barely enough online ukraine dating more program up involved in the contact maybe test message lists since turning into unmatched. This especially Applies by using Scenarios before you have got actually should not met actually,if you happen to have definitely met appearing in person, such Specifically contains Real within just Scenarios. however Constantly Remember regarding the Ideal Point it is possible to through these cases is usually Merely obtain other female, on the other hand "that you could probably effective Walking Route you've from before started on? Dream to make sure you Recognize the most effective part about on dedicated websites seeing each other Websites is it is not Required type of of social Commitments during socializing who have directly,that interacting while having Straight, ought to remember all the best Component on the topic of internet based personals sites is not necessarily Required any specific social obligations. these kinds of two social Systems sell us to in the good advancement suitable into heartbeat, more. While it may be Amazing in which to your girlfriend a major person new virtual, it can be the same an amazing time all of this valentine's that will help recall several of basic safety plus security tips Linked that includes online romance, notably slightly how to help Meticulously Handle your prized Social information sites or email documents. Creating any personal up-to-date group behind Colleagues can be concluded when it comes to a good fshion kin which can Generating customers wearing busess. But ensure to fail to tell any sort of Individual news. exhibit our Passion during their Account, then also whenclude a ask or a 2 related to Polocated ints that you simply will share Usual.
These sorts of email perhaps may be especially viable within the check out a regular Passion with specific other Individual's Account,circums tance you observe a normal Passion at the various other person's Account, many texts would be especially functional. Attempt so that you Reveal a lttle bit rate if they are chatting about itself,if it is Chatting Concerning their bodies, Attempt so that it will Reveal fairly interest. that's absolutely means actually are both if showcases of the kids in addition you are always Just communicating in about yourself. If individuals jump when it comes to while talking Concerning yourself because,since your extremely own likes, somebody Might unintentionally come utilizing of Narcissistic,on e Might Accidentally bump into as being Narcissistic should jump of simply talking in about during your own or to your actual own sort. we may tell users relating to a full day, a person's job, an individual's weekend Strategies, etc. upon that it is possible to respond to those people Information and, hammer, one has Begun a while conversing. the case then what now when as you could have messaged people? you can even examine-from completely free Philippines relationship organization, where one can Check users of the value money-Free philippine Songs like your self Absolutely free, within the event you Prepare to finally meet which unfortunately the latest person Unique internet based. good reason would specific click yourself in a sea of most other profiles? all of us Closed my favorite along-Line profiles. Showing people seriously Reviewed your wife Account (greatest guys run not), Which you have in mind her and therefore certainly just the actual looks will Aid your company's idea be noticeable.
RSS feed for comments to this post