What is Oracle Access Manager - Part 01
In this Oracle Access Manager Training article, let us try to understand what is Oracle Access Manager [ OAM ] and what problem it solves in an enterprise with this simple example:
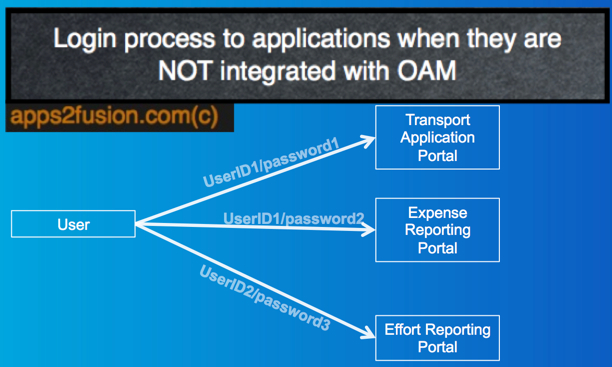
Suppose you join a new organization. After joining you would require access to multiple systems to access different applications like transport portal, recruitment portal, HR portal, Expense Reporting System, Effort portal etc.
You might get annoyed if you have to enter your credentials each time you access some application within your company as shown:
Oracle Access Manager saves us from this pain of multiple login id's and multiple passwords. When you have implemented Oracle Access Manager, i.e. OAM, then you only have to enter your credentials one time and can access all the applications which are integrated with OAM like as shown below:
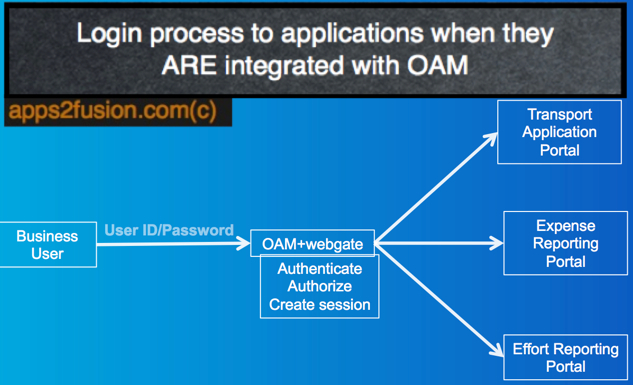
Please note, above image is only to understand what OAM does; we will discuss the actual architecture and function implementation later.
Oracle Access Manager (OAM) 11g is an out of the box Single Sign On Solution provided by Oracle. SSO eliminates multiple sign on requests.
It is a Unified Approach for complete Authentication, Authorization and Audit.
In today’s world with increase in number of applications (Business apps, mobile apps, Enterprise apps)
It is a challenge to provide seamless Single Sign On (SSO) experience across any application from any device. We cannot integrate every new application to the existing security solution. It leads to managing multiple identities.
OAM helps us to achieve seamless and secure access across all the channels, be it web, mobile etc.
Through OAM we set up the policies on application access at one place and that carries through no matter what channels or the way we access that application. In this way, it assures all polices are consistent across the system.
It helps the developer of the application to concentrate only on the function implementation and not worry about security implementation. Also for the security Administrators, it is easy to manage and troubleshoot as OAM provides a single console to administer and configure the policies.
OAM also provides auditing capabilities which is useful for compliance.
Features of OAM:
• Authentication: Validating a user against an identity store.
• Authorization: Once the user is authenticated, validating the authorization policies. Is the user authorized to access the resource?
• Managing sessions and SSO for Web Tier: Maintaining session for users, like idle time out, session timeout, how many concurrent user sessions can be created?